[ad_1]
Quantum resistant cryptography will be a key part of cybersecurity in the future. Here’s what to know about how to protect your data when hackers are armed with quantum computers…
Quantum computing is a contentious topic that people tend to either love or hate depending on where they’re seated. On one hand, it represents an incredible opportunity in terms of data processing speeds and capabilities. On the other, it’s a means through which to destroy the cryptographic algorithms we now rely on to keep sensitive data secure online. This is where something known as quantum resistant encryption comes into play.
But what is quantum resistant encryption? This article explores the history of quantum computing in cryptography, why it’s a threat to modern online security, and what organizations can do to prepare to implement quantum safe cryptography within their IT environments.
Let’s hash it out.
What Is Quantum Resistant Encryption? Explaining Quantum Safe Cryptography
In a nutshell, quantum resistant encryption refers to a set of algorithms that are anticipated to remain secure once quantum computing moves out of the lab and into the real world. (They will replace the public key cryptography algorithms currently used by billions of people around the world every day.)
By the way, when people use any of the following terms, they’re typically talking about the same thing (in most cases):
- Quantum resistant encryption
- Quantum resistant cryptography (QRC)
- Quantum safe cryptography
- Post-quantum cryptography (PQC)
- Post quantum encryption
All of the public key encryption algorithms we currently rely on today are expected to be broken once researchers succeed in building large enough quantum computer. Once that happens, quantum resistant encryption will need to be used everywhere (both by “normal” [i.e., “classical”] and quantum computers) so that attackers with quantum computers can’t break the encryption to steal data.
Why Will Quantum Computers Break Current Encryption Standards?
Quantum computers are fundamentally different from the computers we use today. These devices use specialized hardware components that bring quantum physics into the equation and allows them to perform certain calculations exponentially faster than even the fastest supercomputer we currently have. (We’ll speak to that more later in the article.)
Current public key cryptographic algorithms rely on complex mathematics (for example, the RSA encryption algorithm relies on factoring prime numbers while Diffie-Hellman and elliptic curve cryptography, or ECC, rely on the discrete logarithm problem) to securely transmit data. This means that every time you buy an item on Amazon, your browser communicates with Amazon’s web server via a mathematically derived secure communication channel based on one of these mathematical approaches.
The problem is that some quantum computers will be able to solve these mathematical problems so quickly that hackers would be able to break modern public key encryption within minutes. (Basically, rendering the encryption public key algorithms provide useless.)
According to the National Security Agency (NSA), quantum resistant cryptography should be “resistant to cryptanalytic attacks from both classical and quantum computers.” With this in mind, these algorithms would be something that can be used both before and after quantum computers are put to use in real-world applications. They’re designed with quantum computing threats in mind, but they’re not limited to being used only after a cryptographically relevant quantum computer (CRQC) is created.
Modern Algorithms vs Post Quantum Encryption Algorithms
Currently, encryption over insecure channels (e.g., the internet) relies on something known as public key cryptography. The idea behind traditional public key algorithms is that two parties (i.e., your website’s server and the customer who wants to connect to it) can communicate securely using two separate but related keys: a public key that encrypts data and a private key that decrypts it. They use these keys to exchange secret information that they can use to create a secure, symmetrically encrypted communication channel. (Why symmetric encryption? Because it’s faster and less resource-intensive than public key encryption.)
Unlike modern algorithms, quantum resistant encryption algorithms will replace existing public key specifications with ones that are thought to be quantum resistant. Again, this is because the modern digital signature and key establishment algorithms we rely on in public key encryption now will no longer be secure when CRQCs become a thing.
NIST says that quantum resistant algorithms typically fall in one of three main camps:
- Code-based cryptography — These are algorithms that rely on “error-correcting codes.”
- Lattice-based cryptography — These algorithms involve matrices based on geometric structures.
- Multivariate public key cryptosystems — These types of algorithms vary based on the type of problems they’re trying to solve.
There is a fourth category that some reference — stateful hashed-based signatures. But according to NIST’s PQC FAQs page:
“It is expected that NIST will only approve a stateful hash-based signature standard for use in a limited range of signature applications, such as code signing, where most implementations will be able to securely deal with the requirement to keep state.”
What Would Be Considered a Quantum Resistant Encryption Algorithm?
We can’t give you a specific answer here because, well, nothing has really been decided yet. The National Institute of Standards and Technology (NIST) has been engaged in a large-scale cryptographic competition of sorts for the past several years. The competition is an opportunity for mathematicians, researchers, cryptographers, educators and scientists to submit algorithms for consideration as future federal standards.
The standards body announced their selection of seven candidates and eight alternate algorithm candidates from the third round of submissions. However, no final decisions have been made regarding which algorithm(s) will be standardized:
What Is Quantum Computing?
To better understand quantum resistant encryption and why it’s needed, you first need to understand quantum computers and their anticipated impact on cyber security. The idea behind quantum computing is that these devices use quantum mechanics to approach problem solving — the general goal of all modern computers — in a whole new way and at exponentially faster speeds.
According to research from Mavroeidis, Vishi, Zych, and Jøsang at the University of Oslo, Norway, there are two types of quantum computers:
- Universal quantum computers — As the categorical name implies, these devices are designed to perform virtually any task
- Non-universal quantum computers — These machines are, essentially, designed for specific purposes to handle specific tasks. For some tasks, they aren’t anticipated to be much faster than classical computers.
At a basic level, the computers we use today (classical computers) communicate data using specific combinations of 1s and 0s (binary numbers called bits). All modern computers play by these same rules. For example, if I type the word “Howdy!” the computer uses this combination of bits to communicate the precise combination of keys I press: 01001000 01101111 01110111 01100100 01111001 00100001.

Quantum computers, on the other hand, operate on a new playing field using a different set of rules. Instead of these traditional bits (1s or 0s), it relies on quantum bits, or qubits for short. In a nutshell, instead of looking at either 1s or 0s, quantum computers view data as existing in multiple states, meaning that it can be both 1s and 0s simultaneously (this is known as a superposition). It also uses two other quantum properties — entanglement and interference — to connect separate data elements and eliminate irrelevant guesses to solve problems more quickly.
Of course, not all qubits are the same. Microsoft recently announced that their Azure Quantum program has unlocked the first step to developing a new type of qubit called a topological qubit. The goal is to resolve the scaling-related issues that other quantum computers face and to eventually help lead to the creation of a quantum computer capable of employing one million or more qubits. (Check out the linked article for more information on Microsoft’s demonstration.)
We’re not going to get into all of the technical aspects of the other quantum properties we mentioned here, either. If you want to learn more about superposition, entanglement and interference, check out this video that explains these concepts in a few different ways:
The takeaway we want you to have is that, on one hand, some quantum computers are poised to solve problems beyond what modern supercomputers can do — but faster and more efficiently. They also have the potential for other unimaginable capabilities to do things we haven’t even thought of yet. On the other hand, some quantum computers are anticipated to be no better than classical computers for some types of tasks. But trying to predict the future in terms of the full impact of quantum computers in the future is easier said than done.
Why Quantum Computing Is Thought to Pose a Threat to Modern Cyber Security
Our understanding of quantum computing is largely theoretical — so far, quantum computers can only be used in laboratories due to the machines’ massive resource and cooling requirements. Quantum chips have to be kept super cold (at -273 degrees Celsius, or what amounts to nearly absolute zero) to operate, and they can only operate for very short bursts. But the concern that cybersecurity and industry leaders have is that as quantum computers eventually become more mainstream, they’ll make existing public key encryption algorithms — namely, RSA (Rivest Shamir Adleman) — essentially useless.
This concern is due to a concept known as Shor’s Algorithm. The basic overview of the concern about this algorithm, which was first demonstrated in 1994 by the guy who created it (mathematician Peter Shor), is that a powerful enough quantum computer would be able to crack modern public key algorithms pretty much instantly. How would it do this? By having the ability to calculate the factors of enormous numbers — i.e., the math that operates at the very heart of modern public key encryption — at faster rates than any modern devices could manage.
When you try to crack asymmetric encryption (say, RSA) using a classical computer, you’re essentially trying to guess the factors of those mega-sized integers. As you can imagine, this will take a really long time using a regular computer. But with quantum properties like superposition, entanglement and interference coming into play, it can reduce the time required to make those guesses (or eliminate the need to guess some of the numbers entirely) to basically nothing. For example, while it would take upwards of millions of years for traditional computers to figure out the prime factors of 2,000+ bit numbers, a quantum computer could complete the same task within minutes.
While this enhanced speed will be great for creating positive solutions to problems — such as coming up with revolutionary new treatments or cures for medical conditions — it also poses a problem if these devices fall into the wrong hands.
A Look at the PQC Timeline
Now, we’re not telling you all of this to scare you. The truth is that the threats that quantum computing represents aren’t new concepts, nor do they represent threats to your business and customers right now. The concept of quantum computing — and all of its benefits and dangers — has been around for decades and isn’t expected to come to fruition yet.
Here’s an overview of the history of quantum computing and how the development of quantum resistant cryptography plays a key role in it:
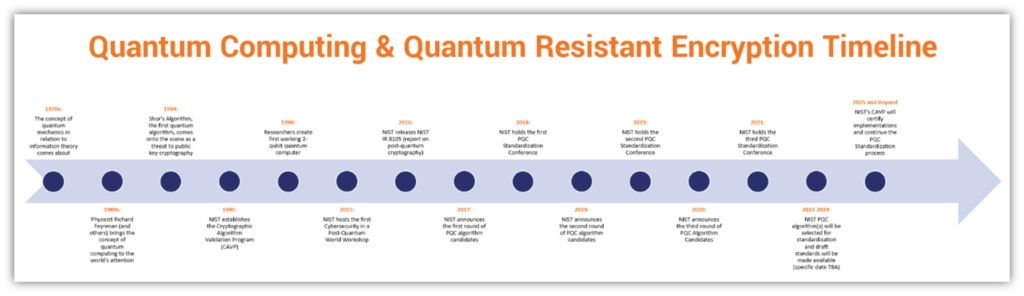
Here are links relating to some of the points on the timeline above:
So, how long is all of this expected to take? The answer depends on who you ask and in what context:
- The National Institute of Standards and Technology (NIST) says it can take 10-20 years “from deciding a cryptosystem is good until we actually get it out there as a disseminated standard in products on the market.”
- The NSA says that “new cryptography can take 20 years or more to be fully developed to all National Security Systems.”
As you’ve probably seen, change tends to be relatively slow in the cryptographic world. Let’s think about it another way. When TLS 1.2 was developed, TLS versions 1.1 and 1.0 were outmoded, but they’re still in use on the web and haven’t gone away completely. (We’re at 14 years and counting at this point since TLS 1.2 was initially released and we now have TLS 1.3, which came out in 2018!)
As we touched on earlier, NIST is working on finalizing the selection of the final algorithms that will become standardized. Once final PQC algorithms are selected, then the next move will be to publish PQC standards as Federal Information Processing Standards (FIPS) and move on to implementations and deployments. Once this occurs, the Cryptographic Algorithm Validation Program (CAPV) will provide certifications for approved implementations of these approved PQC algorithms.
We bring this all up now because we’re drawing closer to a future when quantum computers are anticipated to become mainstream. It won’t happen today, tomorrow, or likely even five years from now. But when it does, organizations will need to be able to support and use the quantum resistant encryption algorithms necessary to help keep data secure in this super-powered computer processing world to come. And things are changing now to prepare for that inevitable future.
A Look at the Changing Landscape Surrounding Quantum Resistant Encryption
On Jan. 19, 2022, the White House released a memorandum specifying that agencies have 180 days to “identify any instances of encryption not in compliance with NSA-approved Quantum-Resistant Algorithms or CNSA […]” and must report the following to the National Manager:
- What systems are noncompliant (including those with exceptions or waivers)
- A timeline for how these systems will transition to compliant encryption, and
- Any reasons why any systems should be exempt from compliance
What does all of this mean at the level of your organization or company? In reality, not much right now for everyday businesses. But let’s be realistic here — it’s virtually impossible to be compliant with rules that haven’t yet been implemented. It’s kind of like playing a new sport — say, soccer — when you don’t yet know the rules or how to play it. Sure, you can go through the motions and move the ball down the field. But if you don’t know how you’re supposed to do it or which goal to aim for specifically, no telling if you’re doing it right or if you’re moving in the right direction.
The National Institute of Standards and Technology (NIST) was anticipating the release of its PQC Round 3 Report by the end of March or early April 2022. (There’s also been talk about announcing a fourth round of study as well.) Now, in all fairness, we’ve just started the month of April a week ago. But considering that agencies are expected to be compliant with quantum-resistant algorithms by basically July 2022, and the algorithms themselves haven’t officially been decided upon… well, that sure makes things a lot more difficult for organizations that have to be compliant.
However, once NIST decides which algorithm(s) will become the standard, then it’s up to businesses and organizations to ensure that they’re not using or relying upon any algorithms that may have been deprecated. The standards body is expected to have draft PQC standards available for public comment before the end of 2023 and aims to have a finalized standard ready the following year.
Although the Sky Isn’t Falling… Yet — Now’s the Time to Prepare
You’ll find that many experts typically sit in one of two camps when it comes to the topic of quantum computing and quantum resistant cryptography. On one end of the spectrum, the first camp — aptly named “Panicville” in the illustration above — essentially operates under the assumption that the end of near! Cybersecurity as we know it is about to come crashing down around us at any moment! BEWARE!
The second camp, which we’ve named “Chillville” in the above graphic, tends to take very different approach. The perspective here is typically that quantum computing is still a long way off, that it’s too impractical for real-world applications, or that it’s something we likely won’t have to deal with for years to come, so there’s no point in worrying about it now.
Needless to say, neither of these approaches is particularly healthy or beneficial to the security of your organization and its data. Thankfully, though, other experts tend to fall somewhere in the middle — let’s call it “Preparationville.” The purveying mindset of experts who sit within this space between the two main camps is that:
- Quantum computing poses a serious threat to modern public key-based security (recognize the threat),
- It’s still going to take a while for this threat to come to life in the real world (stay calm, don’t panic), and
- Organizations should be taking steps now to start getting ready for when it does (make plans and start implementing them now).
Here at Hashed Out, we definitely fall more in the middle of the spectrum; we’re not panicking about the changes to come but are strongly encouraging customers to start preparing now to the best of their abilities. The NSA shares on its Post-Quantum Cybersecurity Resources site that while it doesn’t know “when or even if” a system capable of cracking public key encryption will make its debut. However, it does make it clear that preparing for an “eventual transition” to post-quantum cryptographic standards is a must for data security in the future.
Better to be safe than sorry, right?
It’s Time to Start Preparing for the Inevitable By Planning & Investing In Resources Now
Great. So, you’re being told to prepare, but it’s hard to prepare for something when you don’t really know what tools you’ll have at your disposal to work with. It’s like trying to prepare for a disaster as a homeowner — you might not know when something bad will happen, but you’re going to take steps to mitigate potential impacts as much as possible.
The same concept here applies with preparing for quantum cryptography. While you may not know which algorithms specifically will be standardized, or specifically when quantum resistant cryptography will need to be implemented, you know it’s likely going to happen and that you should take steps now to prepare for it.
Develop Your Organization’s PQC Plan (Be Sure to Include Specific Milestone Dates)
We get it — there’s definitely a strong case of “you don’t know what you don’t know” going on here. However, you can take steps to stay ahead of the curve as much as possible by taking the time to research and plan your strategy now. Part of this planning should include:
- Prioritizing which systems to transition first, starting with the most sensitive and at-risk resources, as well as those that are integral in terms of your organization’s goals and needs
- Designating who is responsible for different aspects of the implementation
Audit Your IT Environment and Cryptographic Systems
We can’t overstate the importance of this task as it’s something you should already be doing anyhow. Auditing your organization’s cryptographic systems, IT infrastructure and applications is crucial for a multitude of reasons. Furthermore, it can aid you as well with the development of your PQC planning and deciding what gets upgraded and when.
Begin Upgrading Your IT Infrastructure and Related Resources
If your organization is running on older servers and other related infrastructure, you’re likely to need to upgrade before quantum cryptography makes its debut. Something to consider includes having servers with redundant distributed databases that use PQC digital signature algorithms that are connected via quantum key distributed (QKD) connections. (QKD is a concept that’s been around since the 80s and involves using quantum mechanics to distribute keys between communicating parties in traditional symmetric algorithm-protected connections.) The idea here is that this may help to protect against quantum attacks and aid in recovery from successful attacks.
What about hardware security modules? Is your organization using one in-house? Is it relying on a third party system? Ensure that whatever HSM you’re using has a roadmap to support quantum safe encryption.
We understand your hesitation and dread — updating your existing infrastructure is a massive undertaking. It involves major investments in money, time, and personnel-related resources. But this is why it’s crucial to start planning for and begin implementing these upgrades now. If you roll out the upgrade to your systems over time, it means you won’t have to blow all of your capital budget in a single year or two, or risk rushing implementation (which can lead to mistakes) because you decided to wait until crap hits the fan.
Essentially, you’re carefully preparing for the impending storm ahead of time (as much as you can). This way, your organization will be less likely to get caught in the downpour others will get swept away in.
Upgrade Your Existing Cryptographic Security Measures
The NSA also offers the Commercial National Security Algorithm Suite (CNSA Suite), which is a set of algorithms that the Committee on National Security Systems Policy 15 (CNSSP-15) has identified for protecting classified information (listed in alphabetical order):
| Algorithm | Key Size / Curve Size | Usage |
| AES-256 | 256 bits | Confidentiality (encryption) |
| Diffie-Helman (DH) | 3072 bits or higher | Key establishment |
| Elliptic Curve Diffie-Hellman (ECDH) | 384 bits | Key establishment |
| ECDSA | 384 bits | Digital signatures |
| Rivest Shamir Adleman (RSA) | 3072 bits or higher | Key establishment and digital signatures |
| SHA-384 | 384 bits | Integrity protection (hashing) |
Broken cryptosystems are the ugly companion of all the advancements that quantum computing has to offer. This is why major certificate authorities like DigiCert and Sectigo are working now to help prepare for a PQC world on their ends by creating PQC certificate authorities (CAs) and certificates.
DigiCert, which plays a key role in multiple PQC projects, offers a PQC Toolkit to Secure Site Pro customers. This toolkit offers hybrid RSA/PQC certificates, which pair PQC algorithms with classical ones. The goal here is for these certificates to work on both legacy systems (to offer backwards compatibility) and quantum systems once quantum computers finally roll out.
DigiCert estimates that it would take a traditional computer “a few quadrillion years” to break modern 2048-bit encryption. But considering that we don’t know exactly when quantum devices are going to come charging onto the scene, it’s a good idea to start preparing now for when it does happen. This is why the CA also has created a resource that breaks down the Post Quantum Cryptography Maturity Model. You can use this to figure out how well prepared your organization is (or isn’t) for what’s the come.
Sectigo’s Senior Vice President of Product Management Lindsay Kent spoke during one of the company’s Identity-First Summit 2022 presentations on certificate lifecycle management. Kent said that the certificate authority expects to have quantum safe security in place by 2026. The plan includes providing customers with a “Quantum Safe Toolkit” as well that aims to help companies:
- Evaluate quantum-safe interoperability with applications
- Create a quantum safe certificate authority to issue certificates using quantum-safe certificate chains
- Issue certificates that can be installed into applications
The goal here for both CAs is to help companies use these certificates to facilitate quantum safe application-based authentication (instead of network-based authentication) and secure communications via TLS sessions. It’s also to ensure that organizations can have certificates in place that support both PQC algorithms and the traditional algorithms that we have in place now.
Wait, doesn’t offering backwards compatibility mean that users on classical devices will still be connecting via protocols relying on insecure algorithms once quantum computers become mainstream? Yes. But if you want to continue providing services to customers using legacy systems, that’s going to continue until they eventually make the change.
Review and Update Your Security Procedures and Protocol Resource Documents
An important part of the planning we talked about earlier is taking the time to review and make changes to your organization’s existing internal security procedures and related documentation. Some of the things you’ll want to consider is what quantum resistant secure access controls and authentication measures you’ll need to implement. As you’ve probably guessed, your existing controls won’t cut it in a PQC world, so everything will need to be updated to be quantum resistant once NIST publishes its standards.
Final Thoughts on Preparing Your Organization to Support Quantum Resistant Encryption
As we talked about earlier, the widespread use of quantum computing — and, therefore, the deployment of quantum resistant cryptography — is still on the horizon but is likely at least a good decade or so away. But that’s why now is the time to prepare for PQC to help your business stay ahead of the curve. You don’t want to be one of the organizations caught unprepared when quantum computers make their mainstream debut.
[ad_2]
Article link